The Dark Web is No Place For Your Company’s Sensitive Data.
The Internet has Layers, One of Which Being the Dark Web.
When you visit the Internet, you are more than likely sticking to the pages that can be accessed by typing an address into your browser, or by clicking on a link in a search result. This is what is known as the surface web, and contains things like:
If a Cybercriminal’s Gone Phishin’, Would Your Employees Take the Bait?
Use Phishing Simulation & Awareness Training to reduce your employees’ risk from phishing and other cyberattacks.
66% of cybercriminals rank email phishing as their attack vector of choice.

Complete Security Solutions for Your Business
The Sophos security apparatus provides organizations with solutions for many of their mission-critical security concerns.
In today's business environment, being able to secure your organization's information and infrastructure is a crucial variable in maintaining the level of company productivity necessary to achieve growth. With Sophos Security solutions offered through JensenIT, you can keep your users, network, and computing infrastructure secure from threats present all over the Internet.
Save Money and Keep Your Company Safe
Eliminate wasted time and money by managing your security from one location.
Standard point-of-service security solutions are highly difficult to institute, update, and manage. This can lead to complex operations and an increase to overhead cost. JensenIT wants to help you eliminate these issues with an All-In-One Security Solution, also known as Unified Threat Management (UTM).
Is Your IT Secure?
Putting it bluntly, you can’t afford to have your IT remain vulnerable in any way that can be avoided. The thing is, managing your security can quickly become excessively complicated. By joining these necessary defenses together into one, singular platform, it becomes far easier for you to maintain them.
We can provide that singular platform for you, helping ensure your business is secure so you can focus on your operations.
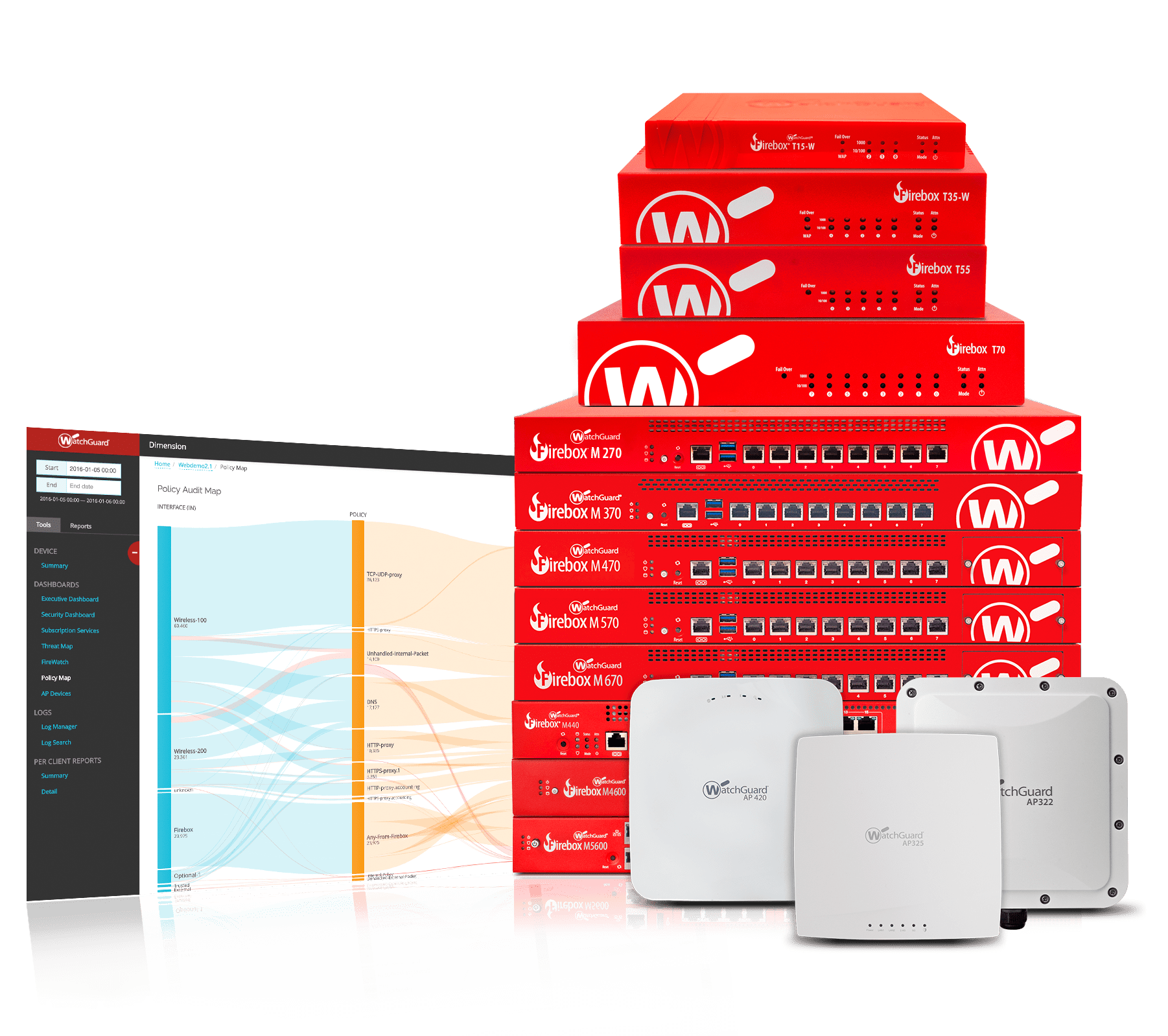
WatchGuard Unified Threat Management
Take control of your network security with a UTM
Your business’ online environment is a prime target for countless threats that want to steal the data of businesses just like yours. Problems such as viruses, malware, and spyware consistently pose massive threats to not just your own network infrastructure, but to your budget as well. Sensitive information that’s stolen can crush your business under the weight of steep compliance fines, while also ruining your reputation as a trustworthy organization.
Let me ask you a question…let’s say that you were in charge of security for some big, fancy event. Would you allow just anyone in, or would you stick to the list of guests that were confirmed as being invited to be there?
 Access Control Solutions
Access Control Solutions
Secure your business with reliable access control solutions from JensenIT.
The IT professionals at JensenIT know that security is crucial for the modern business. That’s why our staff exhaustively works to put together comprehensive risk management strategies that serve today’s business needs. Since many businesses are beginning to turn to technology to secure all aspects of their operations, JensenIT technicians have taken to offering technology-based physical security solutions, as well as solutions that protect an organization’s network and data.
![]()
Protecting your business’ infrastructure where it intersects with your end users.
Cyberattacks Targeting Endpoints Have Risen
Is your business protected where it otherwise would be its most vulnerable?

Mobile Device Management
Start widening the perimeters of business computing with JensenIT's Mobile Device Management system.
Your employees all carry around, and depend on, many types of devices. Smartphones, tablets, Ultrabooks, you name it, they have it. In order to capitalize on this shift in mobile computing, your company needs to enact a Bring Your Own Device policy that protects both your company and your staff. At JensenIT, we have the answer for this necessary integration: our mobile device management solution.

Powerful and secure email protection for you, your clients, and your network.
If you are doing business over today’s Internet, security has to be a priority for your organization.
For those enterprises that could use a platform that provides an additional layer of security for their emails, JensenIT offers a full-scale email encryption solution. Our easily-integrated solution could be the difference between a seemingly benign transmission of information and a debacle that could put your business at risk.

Spam Protection
How much does spam cost your company?
As a business owner, you probably spend a solid amount of time every day checking your email and responding to leads, customers, and employees. Unfortunately, one of the primary faults in email communication is the prevalence of spam. If your organization only works with the bare essentials of spam protection, you’re likely wasting both time and money that could be better spent elsewhere.
Compliance Standards
Ensure that your business adheres to federal, state, and industry regulations
Non-Compliance to Industry Standards Isn’t a Viable Option
Whether they are put in place by federal, state, or industry regulators, compliance standards aren’t something that a business can ignore.
Reveal Vulnerabilities and Meet Compliance with Manual Pen Testing
Even if you’ve invested in the most comprehensive cybersecurity protection, there is no guarantee that a hacker won’t be able to breach your network. Cybercriminals are improving their tactics as quickly as cybersecurity products are being developed. A cyberattack can cause a lot of havoc on your business by crippling your productivity, exposing sensitive information, and damaging your reputation with clients and prospects.
Multi-Factor Authentication
Turn to the solution that can effectively block all automated attacks!
Don’t believe us? Google and Microsoft agree.
Both tech giants have separately gone on the record to talk about the benefits of Multi-Factor Authentication (MFA), stating that their research demonstrated that MFA can block over 99 percent of many attacks. Taking this into consideration, implementing MFA into your own access control features is a no-brainer… especially nowadays.

Surveillance Made Simple
We'll take the headache out of choosing the right surveillance system for your business.
Choosing from the vast amount of surveillance systems available on the market today can be overwhelming to anyone. There's different brands, sizes, and resolutions, along with a lot of options to choose from like motion and light detection.
You want to make sure that when choosing a digital surveillance option that you're not wasting money by purchasing unnecessary equipment, while at the same time, not inhibiting your ability to gain the security you are after. As with many of your technology needs, JensenIT can assist you with this. We've had enough experience in the industry to properly filter through the do's and don'ts, while still keeping future expansion in mind.

Enterprise Mobility Management Solutions
Mobilize your business today.
At JensenIT, we understand that, in some way, mobility is a major pain point of your business. However, enterprise mobility is a comprehensive subject that must address more than just the management of applications on your devices. A Enterprise Mobility Management solution is geared toward helping your organization better understand, manage, and secure your mobile systems. We’ll work with you to ensure that your enterprise mobility management solution keeps your devices in check.

Increase Productivity by Cutting Out Spam
Apply filters to user groups to only allow work related content to be accessed
In order to grow as a company in today’s digital world, you have to provide your employees with resources that make them more efficient. The Internet is one of most important resources your employees will require. Unfortunately, if not controlled properly, granting access to the internet can create its own inefficiencies.

Security Networking
Providing clients with today’s most powerful network and physical security solutions.
For all it gives the modern business, technology gone wrong can ruin everything faster than you can say “Oh, no!” But if you leverage your security the right way, you can protect your network, your data, your physical building, and ultimately everything you and your staff works so hard for. To understand just how important it is for you to have dynamic, well configured security solutions, is to understand the the threats your business faces. JensenIT is Illinois’s tour de force when it comes to business security.
